
“…imagine a world where everything from kitchen appliances, to doorways, to chairs, to potted plants is able to tell you about your customers and their needs. What could your marketing team do if they knew that much more about your audience?”
For marketers, smart devices have opened a whole new set of possibilities we never dreamed of. Interactions through phones, tablets and wearables provide web-enabled apps with time, location, and context to deliver more personalized experiences for everything from news, to social media to shopping — and it works. Why shouldn’t it? Whether your business is a Silicon Valley startup or a university, taking the time to understand your customers and then give them what they want — when they want it — just makes good sense. Now imagine a world where everything from kitchen appliances, to doorways, to chairs, to potted plants is able to tell you about your customers and their needs. What could your marketing team do if they knew that much more about your audience?
Enter the Internet of Things. It sounds like the stuff of fantasy, but the age of IoT is here. If you’ve ever seen a Nest connected thermostat, Canary security system, an iBeacon, or have heard of the Amazon Dash button, you’ve witnessed mass-market IoT in its infancy. And there’s more IoT out there. Way more. Objects in homes, cities, factories, hospitals, cultural centres, retail, are being fitted with sensors at a fantastic rate, all connected and providing organizations with more data on customer activity than ever before. IoT is enabling businesses of all kinds to understand the finer points of their customer experience, and to provide more value — cementing their relationships.
“This is the largest growth in the history of humans,” -Janus Bryzek, “the father of sensors”
Like it or not, IoT will quite literally be everywhere, so your business is going to be affected by it in some way. So we’ve prepared a shortlist of some of the things we help our clients with. Read on, and then contact us to talk IoT strategy.
Things you should start thinking about today:
1. Know your digital customer journey.
What does your customer do before they ever learn about you? What is the first point of contact? What’s the last? What are the digital touchpoints where your audience engages with you? Is it working? A Customer Journey Map can allow you to truly understand where your customers have been, where they’re going, what they want from you, and what they don’t. Taking advantage of the Internet of Things relies on knowing your people. Mapping them out is step one.
2. Analytics. Analytics. Analytics.
It’s one thing to know your customer journey, its another entirely to understand how they interact with you digitally. Analytics can provide not only web interactions (referers, traffic, conversions, bounce rates), but data from social media, CRMs, point-of-sale systems, and more. A custom-tailored analytics dashboard can amalgamate this information into a single point of reference to give you and your teams timely information to drive informed decisions. With the reams of data that can be had through IoT, it’s best to embrace data-driven decision-making and automation soon rather than later.
3. Prepare a modernization strategy.
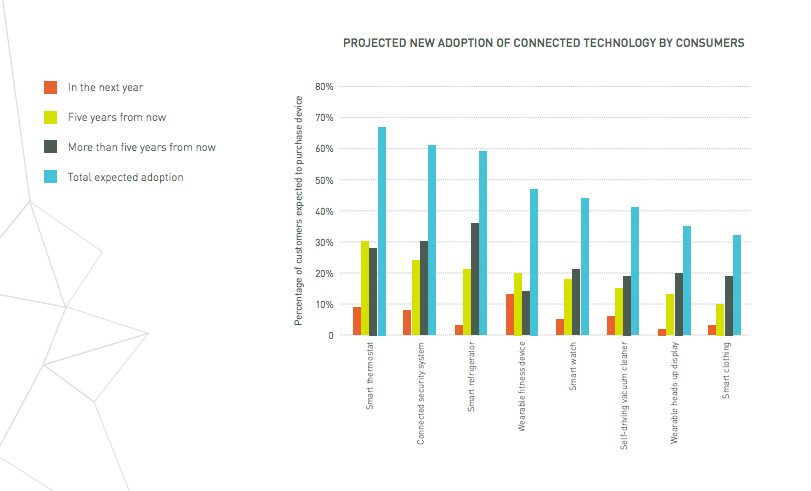
Before you start to embrace The Internet of Things, you’ll need to take an inventory of your digital footprint. A spot-check of our clients shows that more than 50% aren’t using mobile-responsive designs for their websites: there’s no sense in thinking about sensors in lamps if you can’t serve customers on their phones. Take stock of where your digital properties sit with today’s user — both external and in. Audit everything from technology, to SEO, to User Experience. Look at your Journey Map, your analytics, and identify opportunities not only to modernize, but get future-ready. Ask yourself: what ‘things’ are out there that we can use to help our customers? Some places to start are wearables and beacons, but there’s a huge range of open-source sensors and platforms out there that can get you started on a pilot. Even if you never find a use for hardware, you should understand how your customer expectations will change in the coming years, so keep abreast of new advances in IoT and don’t get caught off guard — get it into your strategy and the mindset of your business culture.
Update! September 30, 2015: Think security from the start.
Many thanks to Faud Khan, Chief Security Analyst at TwelveDot for the below input on security and IoT — a hot-button topic that shouldn’t be ignored. From Faud:
The next generation of companies have to think security and privacy day one. Using techniques such as threat modelling and TRAs to understand the risks then evaluating the features that can be added day one verses those that can wait for future revisions. You can always quantify these risks and make better decisions that balance both usability and security.
Here are some quick points to get you started:
- Before you complete your initial product design determine all the cyber and physical aspects that be used to compromise all elements of your solution. This includes the people and suppliers who will come into contact with your product prior to service delivery. This is known a TRA or Technical Risk Assessment these need to into the bits & bites of the solution not just an overview.
- Ensure you have a System Development Lifecycle (SDLC) that includes security. Reference ISO 27034 Application Security as your guide…yes it works with Agile. Get your developers trained and setup to run a formal development and secure testing process. If necessary, use a 3rd party to test the final revision.
- Test for level of assurance you can provide users and customers. Your testers need to be trained on how to locate security bugs in your software as well as dealing with those that are reported to your organization.
- Evaluate all 3rd party libraries for vulnerabilities.
- Make security part of your company culture.
This is just the start of setting up a stringent cyber security program. However, it will make huge strides in getting you on the road to a Secure By Design model.
We’d love to talk IoT with you and help you understand where it fits in your strategy. Reach out to us today to get the conversation started. Better still, if you’re in Ottawa, pay us a visit us at the IoT613 event this week, where our own Brett Tackaberry will be speaking on a panel about The Future of IoT.
 Skip to sharing
Skip to sharing
Thanks, Faud. So much more to say on the topic. Certainly security came to mind. Can you explain ‘attack surface’? I’m sure people will want to know what that is, exactly.