WordPress has recently released a warning of a Cross Site Scripting vulnerability in its code and has urged administers to update their sites immediately. You may have seen this referred to in the media as the “Zero-Day Vulnerability”. The essence of Cross Site Scripting Vulnerabilities is that they can allow malicious code to hijack your login and could take control of your site by injecting code directly into themes and plugins making this a very serious vulnerability that needs to be patched immediately before it can be exploited.
In addition to the WordPress core files being vulnerable, the following plug-ins are also affected:
- Jetpack
- WordPress SEO
- Google Analytics by Yoast
- All In one SEO
- Gravity Forms
- Multiple Plugins from Easy Digital Downloads
- UpdraftPlus
- WP-E-Commerce
- WPTouch
- Download Monitor
- Related Posts for WordPress
- My Calendar
- P3 Profiler
- Give
- Multiple iThemes products including Builder and Exchange
- Broken-Link-Checker
- Ninja Forms
If you are currently running a WordPress site, we strongly urge you to follow the steps in the short primer that follows in order to secure your site.
1. Update all plugins. Log in as the administrator of your account. This login is likely done at www.yoursite.com/wp-admin/
2. The update message should be at the top of the screen as you login.
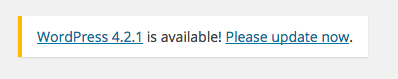
3. Click on “Please Update Now”
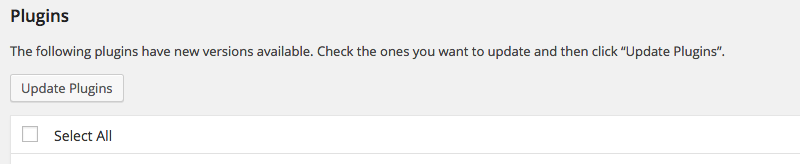
4. Update all your plugins by clicking the “Select All” checkbox and pressing “Update Plugins”
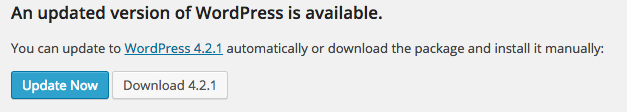
4. Update your WordPress core by pressing “Update Now”
5. Your WordPress is now up to date!
If you have specific concerns about how the Zero-Day vulnerability will affect you, please feel free to call us. Our security staff will be happy to address your concerns and advise you on how you can best protect yourself.
CALL: Extension 378
Ottawa: 613.231.2802 | Montréal: 514.667.0802 | Toronto: 647.723.5456 | Regina: 306.992.4426 | Vancouver: 778.383.7410 or email directly at:security@bv02.com
Looking for more information on the Zero-Day Vulnerability? We’ve complied a list of links below that might answer you questions. Or, if you prefer to talk to someone, feel free to give us a call.
Related Internet links
http://thehackernews.com/2015/04/WordPress-vulnerability.html
http://klikki.fi/adv/wordpress2.html
Photo Credit: Victor Bayon
Skip to sharing